Puntos de control
Provisioning the Kubernetes Engine Cluster
/ 20
Creating the RBAC rules
/ 10
Create server in each namespace
/ 15
Deploying the sample application
/ 20
Fixing the service account name
/ 10
Identifying the application's role and permissions
/ 15
Teardown
/ 10
Cómo usar el control de acceso basado en roles en Kubernetes Engine
- GSP493
- Descripción general
- Arquitectura
- Configuración y requisitos
- Configura tu región y zona
- Tarea 1. Clona la demostración
- Tarea 2. Situación 1: Asignación de permisos por usuario arquetipo
- Tarea 3. Situación 2: Asignación de permisos de API a una aplicación de clúster
- Tarea 4. Elimina
- Tarea 5. Soluciona problemas en tu propio entorno
- ¡Felicitaciones!
GSP493
Descripción general
En este lab, se explica cómo usar y depurar el control de acceso basado en funciones (RBAC) en un clúster de Kubernetes Engine.
Si bien las definiciones de recursos del RBAC son estándar en todas las plataformas de Kubernetes, es necesario entender su interacción con los proveedores de autorización y autenticación subyacentes cuando compila en cualquier proveedor de servicios en la nube.
El RBAC es un mecanismo de seguridad potente que brinda una gran flexibilidad en cuanto a la forma en que se restringen las operaciones dentro de un clúster. En este lab, se presentarán dos casos de uso del RBAC:
- Asignar diferentes permisos a los usuarios arquetipo, es decir, propietarios y auditores
- Otorgar acceso limitado a la API a una aplicación que se ejecuta dentro de tu clúster
Dado que la flexibilidad del RBAC puede, en ocasiones, generar reglas complejas, en la situación 2 se incluyen pasos comunes para la solución de problemas del RBAC.
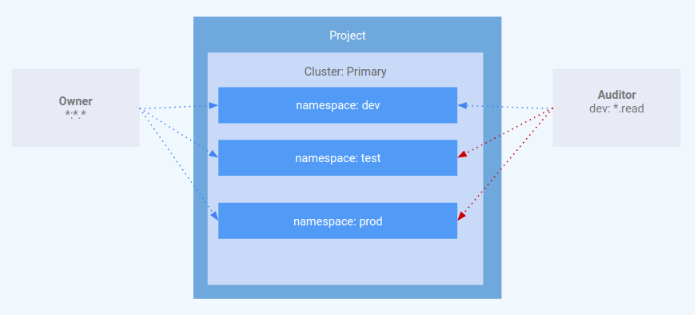
Arquitectura
Este lab se enfoca en el uso del RBAC dentro de un clúster de Kubernetes Engine. Se demuestra cómo se pueden otorgar distintos niveles de privilegios de clúster a diferentes usuarios arquetipo. Aprovisionarás dos cuentas de servicio para representar a los usuarios arquetipo y tres espacios de nombres: desarrollo, prueba y producción. El arquetipo "propietario" tendrá acceso de lectura/escritura a los tres espacios de nombres, mientras que el arquetipo "auditor" tendrá acceso de solo lectura y se lo restringirá al espacio de nombres de desarrollo.
Los ingenieros de GKE Helmsman crearon este lab para ayudarte a comprender mejor cómo usar el control de acceso basado en roles en GKE. Puedes ver esta demostración en GitHub. Te invitamos a hacer cualquier aporte que creas conveniente.
Configuración y requisitos
Antes de hacer clic en el botón Comenzar lab
Lee estas instrucciones. Los labs son cronometrados y no se pueden pausar. El cronómetro, que comienza a funcionar cuando haces clic en Comenzar lab, indica por cuánto tiempo tendrás a tu disposición los recursos de Google Cloud.
Este lab práctico te permitirá realizar las actividades correspondientes en un entorno de nube real, no en uno de simulación o demostración. Para ello, se te proporcionan credenciales temporales nuevas que utilizarás para acceder a Google Cloud durante todo el lab.
Para completar este lab, necesitarás lo siguiente:
- Acceso a un navegador de Internet estándar (se recomienda el navegador Chrome)
- Tiempo para completar el lab: Recuerda que, una vez que comienzas un lab, no puedes pausarlo.
Cómo iniciar su lab y acceder a la consola de Google Cloud
-
Haga clic en el botón Comenzar lab. Si debe pagar por el lab, se abrirá una ventana emergente para que seleccione su forma de pago. A la izquierda, se encuentra el panel Detalles del lab que tiene estos elementos:
- El botón Abrir la consola de Google
- Tiempo restante
- Las credenciales temporales que debe usar para el lab
- Otra información para completar el lab, si es necesaria
-
Haga clic en Abrir la consola de Google. El lab inicia recursos y abre otra pestaña en la que se muestra la página de acceso.
Sugerencia: Ordene las pestañas en ventanas separadas, una junto a la otra.
Nota: Si ve el diálogo Elegir una cuenta, haga clic en Usar otra cuenta. -
Si es necesario, copie el nombre de usuario del panel Detalles del lab y péguelo en el cuadro de diálogo Acceder. Haga clic en Siguiente.
-
Copie la contraseña del panel Detalles del lab y péguela en el cuadro de diálogo de bienvenida. Haga clic en Siguiente.
Importante: Debe usar las credenciales del panel de la izquierda. No use sus credenciales de Google Cloud Skills Boost. Nota: Usar su propia Cuenta de Google podría generar cargos adicionales. -
Haga clic para avanzar por las páginas siguientes:
- Acepte los términos y condiciones.
- No agregue opciones de recuperación o autenticación de dos factores (esta es una cuenta temporal).
- No se registre para obtener pruebas gratuitas.
Después de un momento, se abrirá la consola de Cloud en esta pestaña.

Activa Cloud Shell
Cloud Shell es una máquina virtual que cuenta con herramientas para desarrolladores. Ofrece un directorio principal persistente de 5 GB y se ejecuta en Google Cloud. Cloud Shell proporciona acceso de línea de comandos a tus recursos de Google Cloud.
- Haz clic en Activar Cloud Shell
en la parte superior de la consola de Google Cloud.
Cuando te conectes, habrás completado la autenticación, y el proyecto estará configurado con tu PROJECT_ID. El resultado contiene una línea que declara el PROJECT_ID para esta sesión:
gcloud es la herramienta de línea de comandos de Google Cloud. Viene preinstalada en Cloud Shell y es compatible con la función de autocompletado con tabulador.
- Puedes solicitar el nombre de la cuenta activa con este comando (opcional):
-
Haz clic en Autorizar.
-
Ahora, el resultado debería verse de la siguiente manera:
Resultado:
- Puedes solicitar el ID del proyecto con este comando (opcional):
Resultado:
Resultado de ejemplo:
gcloud, consulta la guía con la descripción general de gcloud CLI en Google Cloud.
Configura tu región y zona
Algunos recursos de Compute Engine se encuentran en regiones y zonas. Una región es una ubicación geográfica específica donde puedes ejecutar tus recursos. Cada región tiene una o más zonas.
Ejecuta el siguiente comando para configurar una región y zona para tu lab (puedes usar la región/zona más adecuada para tu caso):
Tarea 1. Clona la demostración
- Ejecuta el siguiente comando para clonar los recursos que se necesitarán en este lab:
- Cambia al directorio extraído:
Aprovisiona el clúster de Kubernetes Engine
A continuación, aplica la configuración de Terraform.
- Desde el directorio raíz del proyecto, ejecuta el comando
makepara aplicar la configuración de Terraform:
La configuración de esta demostración lleva entre 10 y 15 minutos. Si no hay un error, lo mejor es seguir esperando. No debe interrumpirse la ejecución de make create.
- Mientras se compilan los recursos, cuando veas que se creó
google_compute_instance, podrás verificar el progreso en en Console. Para ello, ve a Compute Engine > Instancias de VM. En la página Instancias de VM, consulta la información más actualizada con el botón Actualizar.
Cuando finalice la implementación, Terraform mostrará un mensaje que indica que el clúster se creó correctamente.
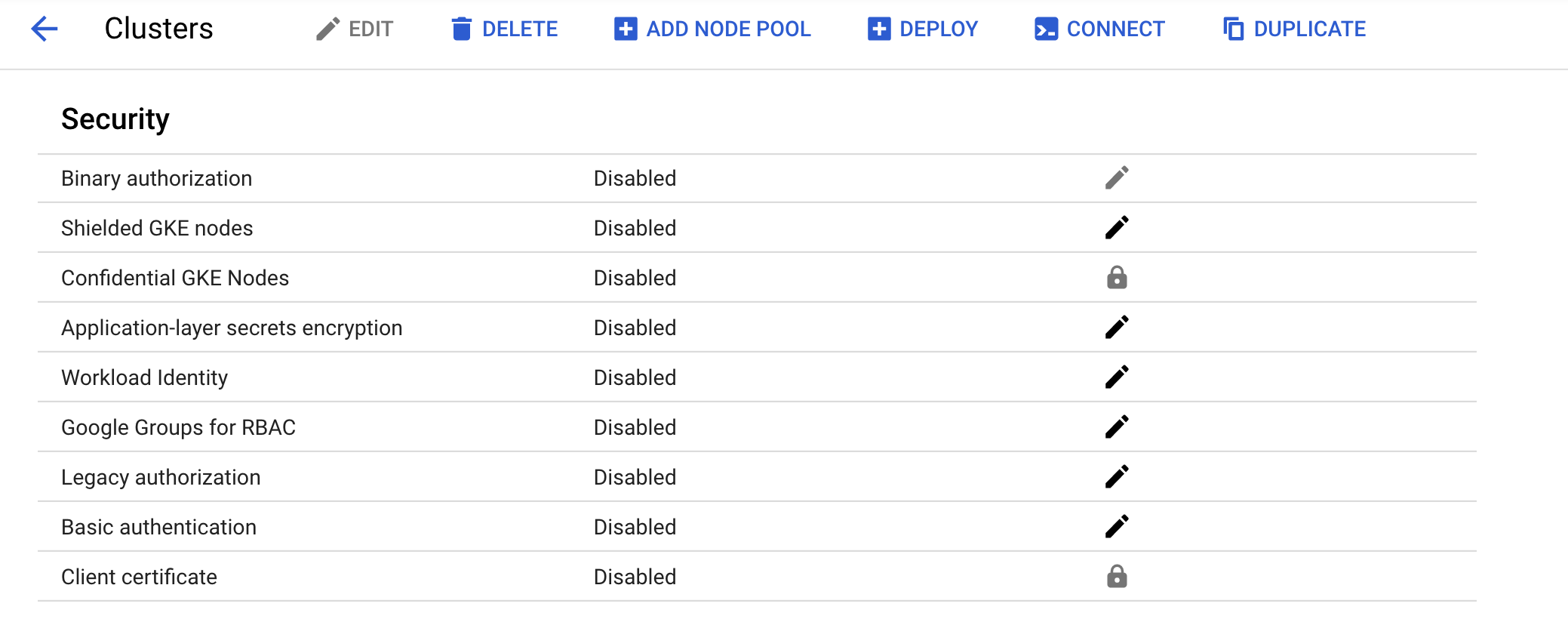
- En Console, confirma que el clúster se haya creado correctamente. Ve a Menú de navegación > Kubernetes Engine > Clústeres y haz clic en el clúster que se creó. Asegúrate de que esté inhabilitada la autorización heredada para el nuevo clúster.
Haz clic en Revisar mi progreso para verificar el objetivo.
Tarea 2. Situación 1: Asignación de permisos por usuario arquetipo
Rol de IAM
Se creó un rol llamado kube-api-ro-xxxxxxxx (en el que xxxxxxxx es una cadena aleatoria) con los siguientes permisos como parte de la configuración de Terraform en iam.tf. Estos son los permisos mínimos necesarios para cualquier usuario que requiera acceso a la API de Kubernetes.
- container.apiServices.get
- container.apiServices.list
- container.clusters.get
- container.clusters.getCredentials
Simula usuarios
Se crearon tres cuentas de servicio para que actúen como usuarios de prueba:
- administrador: tiene permisos de administrador sobre el clúster y todos los recursos.
- propietario: tiene permisos de lectura y escritura sobre los recursos comunes del clúster.
- auditor: tiene permisos de solo lectura únicamente dentro del espacio de nombres de desarrollo.
- Ejecuta este comando:
La secuencia de comandos de Terraform aprovisionó tres hosts de prueba. En cada nodo, se instaló y configuró kubectl y gcloud para simular un usuario arquetipo diferente.
- gke-tutorial-admin: kubectl y gcloud se autenticaron como administradores del clúster.
-
gke-tutorial-owner: simula la cuenta
owner -
gke-tutorial-auditor: simula la cuenta
auditor
- Ejecuta este comando:
Resultado:
Crea las reglas de RBAC
Crea los espacios de nombres, roles y vinculaciones de roles iniciando sesión en la instancia de administrador y aplicando el manifiesto rbac.yaml.
- Establece una conexión SSH al administrador:
Las versiones existentes de kubectl y los clientes personalizados de Kubernetes contienen código específico del proveedor para administrar la autenticación entre el cliente y Google Kubernetes Engine. A partir de la versión 1.26, este código ya no se incluirá como parte del software de código abierto de kubectl. Los usuarios de GKE deberán descargar y usar un complemento de autenticación independiente para generar tokens específicos de GKE. Este nuevo objeto binario, gke-gcloud-auth-plugin, usa el mecanismo Complemento de credenciales Client-go de Kubernetes para extender la autenticación de kubectl y respaldar GKE. Para obtener más información, revisa la siguiente documentación.
Sigue estos pasos para que kubectl use el nuevo complemento de objeto binario para la autenticación, en lugar del código específico del proveedor.
- Luego de conectarte, ejecuta el siguiente comando para instalar el
gke-gcloud-auth-pluginen la VM.
- Establece
export USE_GKE_GCLOUD_AUTH_PLUGIN=Trueen~/.bashrc:
- Ejecuta el siguiente comando:
- Ejecuta este comando para forzar la configuración de este clúster, de manera que se actualice a la configuración del Complemento de credenciales Client-go.
Si la operación es exitosa, deberías ver este mensaje emergente:
El clúster recién creado estará disponible para los comandos estándar de kubectl en el host de bastión.
- Crea los espacios de nombres, roles y vinculaciones:
Resultado:
Haz clic en Revisar mi progreso para verificar el objetivo.
Administra los recursos como propietario
- En la parte superior de la ventana de terminal, haz clic en + para abrir una terminal nueva de Cloud Shell.
A continuación, establecerás una conexión SSH a la instancia de propietario y crearás una implementación simple en cada espacio de nombres.
- Establece una conexión SSH a la instancia de propietario:
-
Cuando se te pregunte acerca de la zona, ingresa
npara que se use la zona predeterminada. -
Instala gke-gcloud-auth-plugin:
- Crea un servidor en cada espacio de nombres; primero, en
dev:
Resultado:
- Luego, crea un servidor en
prod:
Resultado:
- Por último, crea un servidor en el espacio de nombres
test:
Resultado:
Haz clic en Revisar mi progreso para verificar el objetivo.
Como propietario, también podrás ver todos los Pods.
- En la instancia de propietario, ejecuta el siguiente comando para enumerar los Pods
hello-serveren todos los espacios de nombres:
Resultado:
Visualiza los recursos como auditor
Ahora, abrirás una terminal nueva, establecerás una conexión SSH a la instancia de auditor y, luego, intentarás visualizar todos los espacios de nombres.
-
En la parte superior de la ventana de terminal, haz clic en + para abrir una terminal nueva de Cloud Shell.
-
Establece una conexión SSH a la instancia de auditor:
-
Cuando se te pregunte acerca de la zona, ingresa
npara que se use la zona predeterminada. -
Instala gke-gcloud-auth-plugin:
- En la instancia de auditor, ejecuta el siguiente comando para enumerar los Pods
hello-serveren todos los espacios de nombres:
Deberías ver un error como el siguiente:
El error indica que no tienes permisos suficientes. La función de auditor se restringió al espacio de nombres de desarrollo y tiene acceso de solo lectura, por lo que deberás especificar el espacio de nombres cuando visualices los recursos.
Ahora intenta visualizar los Pods en el espacio de nombres de desarrollo.
- En la instancia de auditor, ejecuta el siguiente comando:
Resultado:
- Intenta visualizar los Pods en el espacio de nombres de prueba:
Resultado:
- Intenta visualizar los Pods en el espacio de nombres de producción:
Resultado:
Por último, intenta crear y borrar una implementación en el espacio de nombres de desarrollo para verificar que el auditor tenga acceso de solo lectura.
- En la instancia de auditor, intenta crear una implementación:
Resultado:
- En la instancia de auditor, intenta borrar la implementación:
Resultado:
Tarea 3. Situación 2: Asignación de permisos de API a una aplicación de clúster
En esta situación, seguirás el proceso para implementar una aplicación que requiera acceso a la API de Kubernetes y configurarás las reglas de RBAC mientras solucionas problemas de algunos casos de uso comunes.
Implementa la aplicación de prueba
La aplicación de prueba se ejecutará como un solo Pod que recupera, de forma periódica, todos los Pods en el espacio de nombres predeterminado del servidor de API y, luego, aplica una etiqueta de marca de tiempo a cada uno.
- Desde la instancia admin (este debería ser tu primer tab de Cloud Shell), implementa la aplicación
pod-labeler. Con esta acción, también se implementará un objeto Role, ServiceAccount y RoleBinding en el Pod:
Resultado:
Haz clic en Revisar mi progreso para verificar el objetivo.
Diagnostica una configuración incorrecta de RBAC
Ahora verifica el estado del Pod. Una vez que se haya creado el contenedor, verás un error. Inspecciona los eventos y registros de los Pods para investigar el error.
- En la instancia admin verifica el estado de los pods:
Resultado:
- En la instancia admin visualiza el flujo de eventos del pod ejecutando:
Deberías ver lo siguiente:
- En la instancia admin ejecuta lo siguiente para verificar los registros del pod:
Resultado:
Según este resultado, puedes ver un error de permisos cuando intentas enumerar los Pods a través de la API.
- El siguiente paso consiste en confirmar que utilizas el objeto ServiceAccount correcto.
Corrige serviceAccountName
Al inspeccionar la configuración del Pod, puedes ver que usa el objeto ServiceAccount predeterminado en lugar del objeto ServiceAccount personalizado.
- En la instancia admin ejecuta:
Resultado:
El archivo pod-labeler-fix-1.yaml contiene la solución en la especificación de la plantilla de la implementación:
A continuación, aplicarás la solución y verás el cambio resultante.
- En la instancia admin aplica la solución 1 ejecutando:
Resultado:
- Ve el cambio en la configuración de implementación:
Cambios en el resultado:
Haz clic en Revisar mi progreso para verificar el objetivo.
Diagnostica privilegios insuficientes
Una vez más, verifica el estado de tu Pod y notarás que todavía tiene un error, pero esta vez el mensaje es diferente.
- En la instancia admin, verifica el estado de tu pod:
Resultado:
Es posible que debas volver a ejecutar el comando anterior para ver este resultado.
- En la instancia admin verifica los registros del pod:
Resultado:
Dado que la falla se presenta en una operación de PATCH, también puedes ver el error en Stackdriver. Esto es útil si los registros de la aplicación no son lo suficientemente detallados.
-
En la consola, selecciona Menú de navegación y, en la sección Operaciones, haz clic en Logging.
-
En el cuadro de diálogo del Compilador de consultas, pega el siguiente código y haz clic en Ejecutar consulta (Run Query):
- Haz clic en alguna flecha hacia abajo que se encuentre junto a un registro y explora los detalles.
Identifica el rol función y los permisos de la aplicación
Usa el objeto ClusterRoleBinding para averiguar el rol y los permisos de ServiceAccount.
- En la instancia admin inspecciona la definición del objeto
rolebinding:
Resultado:
El objeto RoleBinding muestra que debes inspeccionar el rol pod-labeler en el espacio de nombres predeterminado. Aquí, podrás ver que el rol solo tiene permiso para enumerar Pods.
- En la instancia admin inspecciona la definición del rol
pod-labeler:
Resultado:
Dado que la aplicación requiere permisos de PATCH, puedes agregarla a la lista de "verbos" del rol, y eso es lo que harás a continuación.
El archivo pod-labeler-fix-2.yaml contiene la solución en la sección de reglas y verbos:
Aplica la solución y verás la configuración resultante.
- En la instancia de admin aplica
fix-2:
Resultado:
Haz clic en Revisar mi progreso para verificar el objetivo.
- En la instancia de admin visualiza el cambio resultante:
Resultado:
Dado que pod-labeler puede estar en un bucle de retroceso, la forma más rápida de probar la solución es eliminar el Pod existente y dejar que uno nuevo ocupe su lugar.
- En la instancia de administrador, ejecuta el siguiente comando para eliminar el Pod existente y dejar que el controlador de implementación lo reemplace:
Resultado:
Verifica si se realizó correctamente la configuración
Por último, verifica que se esté ejecutando el pod-labeler nuevo y que se haya aplicado la etiqueta "updated".
- En la instancia de admin enumera todos los Pods y muestra sus etiquetas:
Resultado:
- Consulta los registros del Pod para verificar que ya no haya errores:
Resultado:
Conclusiones principales
- Los registros del servidor de la API y de los contenedores son la mejor fuente de información para diagnosticar problemas de RBAC.
- Usa objetos RoleBinding o ClusterRoleBinding para determinar qué función especifica los permisos para un Pod.
- Los registros del servidor de la API se pueden encontrar en Stackdriver, en el recurso Kubernetes.
- No todas las llamadas a la API se registrarán en Stackdriver. La política de auditoría de Kubernetes que usa Kubernetes Engine omite las cargas útiles frecuentes o detalladas. La política exacta variará según la versión de Kubernetes, pero se puede encontrar en la base de código abierto.
Tarea 4. Elimina
Cuando termines y tengas todo listo para limpiar los recursos que se crearon, ejecuta el siguiente comando para quitarlos:
-
Cierra la sesión del host de bastión escribiendo
exit. -
Ejecuta el siguiente comando para destruir el entorno:
Resultado:
Haz clic en Revisar mi progreso para verificar el objetivo.
Tarea 5. Soluciona problemas en tu propio entorno
Cuando se ejecuta Terraform, la secuencia de comandos de instalación falla y muestra el mensaje Permission denied
Las credenciales que usa Terraform no proporcionan los permisos necesarios para crear recursos en los proyectos seleccionados. Asegúrate de que la cuenta que se detalla en gcloud config list tenga los permisos necesarios para crear recursos. Si los tienes, vuelve a generar las credenciales predeterminadas de la aplicación con gcloud auth application-default login.
Error de huella digital no válida durante las operaciones de Terraform
En ocasiones, Terraform emite un mensaje de error de huella digital no válida al actualizar ciertos recursos. Vuelve a ejecutar el comando si obtienes un error con el mensaje: Error: Error applying plan y, a continuación, se enumeran estos errores:
module.network.google_compute_subnetwork.cluster-subnet: 1 error(s) occurredgoogle.compute_subnetwork.cluster-subnet: Error updating subnetwork/kube-net-subnet: googleapi: Error412: Invalid fingerprint, conditionNotMet
¡Felicitaciones!
Exploraste el control de acceso basado en roles (RBAC): asignaste diferentes permisos a diferentes usuarios arquetipo y otorgaste acceso limitado a la API a una aplicación que se ejecuta en tu clúster.
Finaliza tu Quest
Este lab de autoaprendizaje es parte de la Quest Google Kubernetes Engine Best Practices: Security. Una Quest es una serie de labs relacionados que forman una ruta de aprendizaje. Si completas esta Quest, obtendrás una insignia como reconocimiento por tu logro. Puedes hacer públicas tus insignias y agregar vínculos a ellas en tu currículum en línea o en tus cuentas de redes sociales. Inscríbete en esta Quest o en cualquiera que contenga este lab y obtén un crédito inmediato de finalización. Consulta el catálogo de Google Cloud Skills Boost para ver todas las Quests disponibles.
Realiza tu próximo lab
Continúa tu Quest con Seguridad de Google Kubernetes Engine: Autorización binaria, o consulta lo siguiente:
Próximos pasos/Más información
- Configura el control de acceso basado en roles
- Crea políticas de IAM
- Autenticación de la cuenta de servicio de Kubernetes
- Documentación de Terraform
Capacitación y certificación de Google Cloud
Recibe la formación que necesitas para aprovechar al máximo las tecnologías de Google Cloud. Nuestras clases incluyen habilidades técnicas y recomendaciones para ayudarte a avanzar rápidamente y a seguir aprendiendo. Para que puedas realizar nuestros cursos cuando más te convenga, ofrecemos distintos tipos de capacitación de nivel básico a avanzado: a pedido, presenciales y virtuales. Las certificaciones te ayudan a validar y demostrar tus habilidades y tu conocimiento técnico respecto a las tecnologías de Google Cloud.
Última actualización del manual: 9 de octubre de 2023
Prueba más reciente del lab: 9 de octubre de 2023
Copyright 2024 Google LLC. Este software se proporciona tal como está, sin garantías ni declaraciones para ningún uso o propósito. El uso que hagas de él está sujeto a tu acuerdo con Google.