Checkpoints
Provisioning the Kubernetes Engine Cluster
/ 20
Creating the RBAC rules
/ 10
Create server in each namespace
/ 15
Deploying the sample application
/ 20
Fixing the service account name
/ 10
Identifying the application's role and permissions
/ 15
Teardown
/ 10
Como usar o controle de acesso baseado em função no Kubernetes Engine
- GSP493
- Visão geral
- Arquitetura
- Configuração e requisitos
- Configure sua região e zona
- Tarefa 1: clonar a demonstração
- Tarefa 2: Cenário 1: atribuir permissões por perfil de usuário
- Tarefa 3: Cenário 2: atribuir permissões de API a um aplicativo de cluster
- Tarefa 4: Eliminação
- Tarefa 5: Solução de problemas no seu ambiente
- Parabéns!
GSP493
Visão geral
Este laboratório aborda o uso e a depuração do controle de acesso baseado em funções (RBAC) em um cluster do Kubernetes Engine.
Embora as definições de recursos do RBAC sejam padrão em todas as plataformas Kubernetes, você precisa entender sua interação com os provedores de autenticação e autorização subjacentes ao criar em qualquer provedor de nuvem.
O RBAC é um mecanismo de segurança avançado que proporciona muitas formas de restringir as operações em um cluster. Este laboratório abrange dois casos de uso do RBAC:
- Como atribuir permissões diferentes a perfis de usuários, ou seja, proprietários e auditores.
- Como conceder acesso de API limitado a um aplicativo em execução no cluster.
Como a flexibilidade do RBAC às vezes pode resultar em regras complexas, apresentamos etapas comuns para solucionar problemas do RBAC no cenário 2.
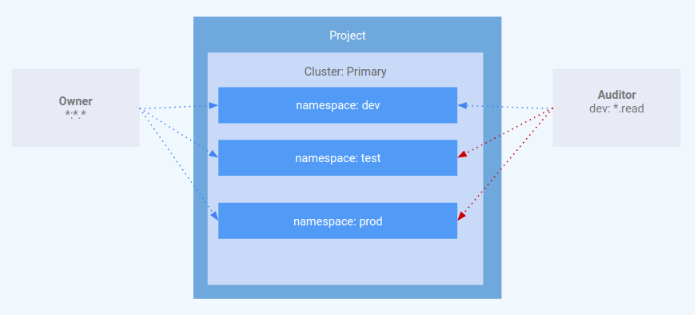
Arquitetura
Este laboratório explica o uso do RBAC em um cluster do Kubernetes Engine. Ele mostra como conceder vários níveis de privilégio de cluster a perfis de usuário diferentes. Você provisionará duas contas de serviço para representar os perfis de usuário e três namespaces: "dev", "test" e "prod". O perfil "owner" terá acesso de leitura/gravação aos três namespaces, já o perfil "auditor" terá acesso somente leitura ao namespace "dev".
Este laboratório foi criado por engenheiros do GKE Helmsman para explicar o uso dos controles de acesso baseado em função no GKE. Confira esta demonstração no GitHub. Incentivamos todos a contribuir com nossos recursos.
Configuração e requisitos
Antes de clicar no botão Start Lab
Leia estas instruções. Os laboratórios são cronometrados e não podem ser pausados. O timer é iniciado quando você clica em Começar o laboratório e mostra por quanto tempo os recursos do Google Cloud vão ficar disponíveis.
Este laboratório prático permite que você realize as atividades em um ambiente real de nuvem, não em uma simulação ou demonstração. Você vai receber novas credenciais temporárias para fazer login e acessar o Google Cloud durante o laboratório.
Confira os requisitos para concluir o laboratório:
- Acesso a um navegador de Internet padrão (recomendamos o Chrome).
- Tempo para concluir o laboratório---não se esqueça: depois de começar, não será possível pausar o laboratório.
Como iniciar seu laboratório e fazer login no console do Google Cloud
-
Clique no botão Começar o laboratório. Se for preciso pagar, você verá um pop-up para selecionar a forma de pagamento. No painel Detalhes do laboratório à esquerda, você verá o seguinte:
- O botão Abrir Console do Cloud
- Tempo restante
- As credenciais temporárias que você vai usar neste laboratório
- Outras informações se forem necessárias
-
Clique em Abrir Console do Google. O laboratório ativa recursos e depois abre outra guia com a página Fazer login.
Dica: coloque as guias em janelas separadas lado a lado.
Observação: se aparecer a caixa de diálogo Escolher uma conta, clique em Usar outra conta. -
Caso seja preciso, copie o Nome de usuário no painel Detalhes do laboratório e cole esse nome na caixa de diálogo Fazer login. Clique em Avançar.
-
Copie a Senha no painel Detalhes do laboratório e a cole na caixa de diálogo Olá. Clique em Avançar.
Importante: você precisa usar as credenciais do painel à esquerda. Não use suas credenciais do Google Cloud Ensina. Observação: se você usar sua própria conta do Google Cloud neste laboratório, é possível que receba cobranças adicionais. -
Acesse as próximas páginas:
- Aceite os Termos e Condições.
- Não adicione opções de recuperação nem autenticação de dois fatores (porque essa é uma conta temporária).
- Não se inscreva em testes gratuitos.
Depois de alguns instantes, o console do GCP vai ser aberto nesta guia.

Ativar o Cloud Shell
O Cloud Shell é uma máquina virtual com várias ferramentas de desenvolvimento. Ele tem um diretório principal permanente de 5 GB e é executado no Google Cloud. O Cloud Shell oferece acesso de linha de comando aos recursos do Google Cloud.
- Clique em Ativar o Cloud Shell
na parte de cima do console do Google Cloud.
Depois de se conectar, vai notar que sua conta já está autenticada, e que o projeto está configurado com seu PROJECT_ID. A saída contém uma linha que declara o projeto PROJECT_ID para esta sessão:
gcloud é a ferramenta de linha de comando do Google Cloud. Ela vem pré-instalada no Cloud Shell e aceita preenchimento com tabulação.
- (Opcional) É possível listar o nome da conta ativa usando este comando:
-
Clique em Autorizar.
-
A saída será parecida com esta:
Saída:
- (Opcional) É possível listar o ID do projeto usando este comando:
Saída:
Exemplo de saída:
gcloud, acesse o guia com informações gerais sobre a gcloud CLI no Google Cloud.
Configure sua região e zona
Alguns recursos do Compute Engine estão em regiões e zonas. As regiões são localizações geográficas específicas onde você executa seus recursos. Todas elas têm uma ou mais zonas.
Execute o comando a seguir para configurar a região e a zona do seu laboratório (use a região/zona mais adequada para você):
Tarefa 1: clonar a demonstração
- Faça o download dos recursos necessários para este laboratório executando o seguinte:
- Mude para o diretório extraído:
Provisionar o cluster do Kubernetes Engine
Aplique a configuração do Terraform.
- Na raiz do projeto, use
makepara aplicar a configuração do Terraform:
A configuração da demonstração leva de 10 a 15 minutos. Caso não haja erros, o melhor a fazer é esperar. A execução de make create não deve ser interrompida.
- Nesse período, após a criação de
google_compute_instance, verifique o progresso no console acessando Compute Engine > Instâncias de VM. Nessa página, use o botão Atualizar para ver informações mais atualizadas.
Após a conclusão, o Terraform mostra uma mensagem indicando a criação do cluster.
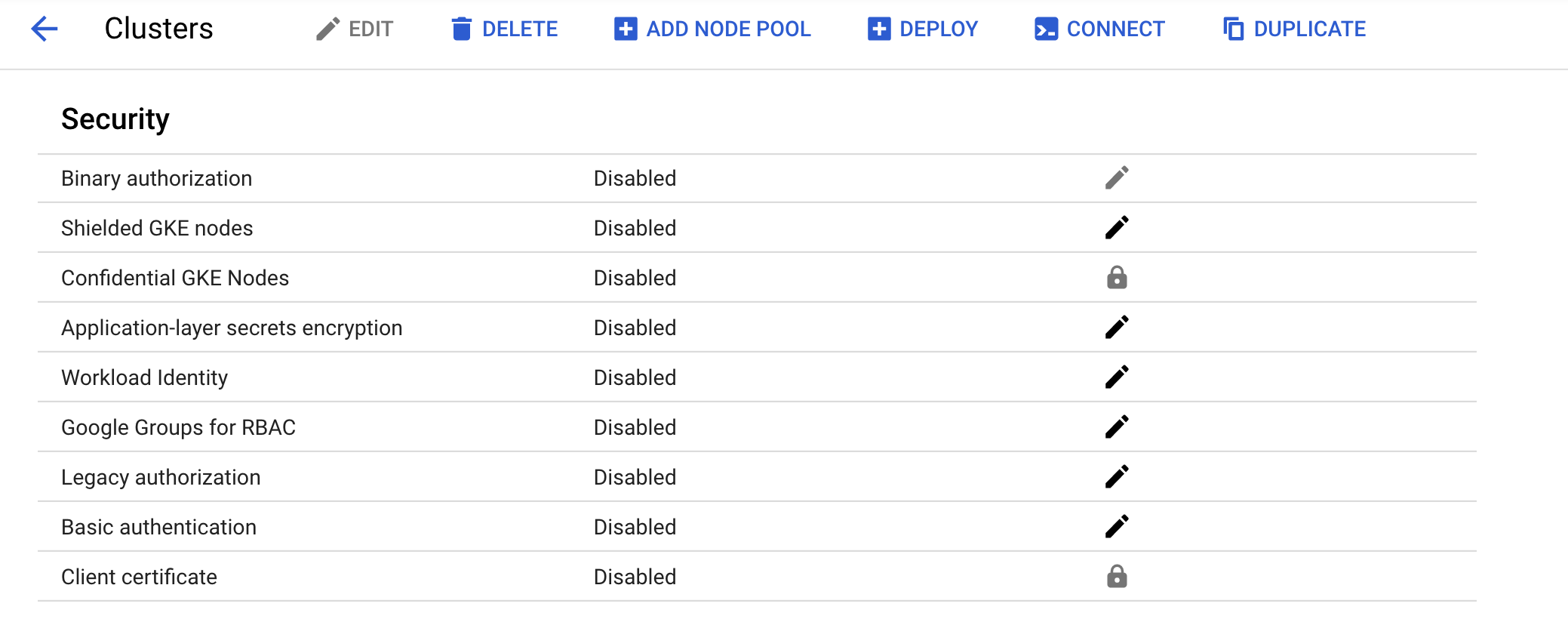
- Confirme se o cluster foi criado corretamente no console. Acesse Menu de navegação > Kubernetes Engine > Clusters e clique no cluster criado. Verifique se a autorização legada está desativada no novo cluster.
Clique em Verificar meu progresso para conferir o objetivo.
Tarefa 2: Cenário 1: atribuir permissões por perfil de usuário
IAM - papel
Um papel chamado kube-api-ro-xxxxxxxx (em que xxxxxxxx é uma string aleatória) foi criado com as permissões abaixo como parte da configuração do Terraform em iam.tf. Essas permissões representam o mínimo necessário para qualquer usuário que precise acessar a API Kubernetes.
- container.apiServices.get
- container.apiServices.list
- container.clusters.get
- container.clusters.getCredentials
Como simular usuários
Três contas de serviço foram criadas como usuários de teste:
- admin: tem permissões de administrador no cluster e em todos os recursos
- owner: tem permissões de leitura e gravação nos recursos de cluster comuns
- auditor: tem permissões somente leitura no namespace "dev"
- Execute o comando a seguir:
Três hosts de teste foram provisionados pelo script do Terraform. Cada nó tem o kubectl e o gcloud instalados e configurados para simular um perfil de usuário diferente.
- gke-tutorial-admin: kubectl e gcloud são autenticados como administradores de cluster.
-
gke-tutorial-owner: simula a conta
owner. -
gke-tutorial-auditor: simula a conta
auditor.
- Execute o comando a seguir:
Saída:
Criar as regras do RBAC
Para criar os namespaces, os papéis e as vinculações de papéis, faça login na instância do administrador e aplique o manifesto rbac.yaml.
- Estabeleça conexão SSH com a instância "admin":
As versões atuais do kubectl e dos clientes personalizados do Kubernetes contêm código específico do provedor para gerenciar a autenticação entre o cliente e o Google Kubernetes Engine. A partir da versão 1.26, esse código não vai mais ser incluído como parte do OSS kubectl. Os usuários do GKE vão precisar fazer o download e usar um plug-in de autenticação separado para gerar tokens específicos do GKE. O novo binário, gke-gcloud-auth-plugin, usa o mecanismo do plug-in de credenciais do cliente Go do Kubernetes para ampliar a autenticação do kubectl e oferecer suporte ao GKE. Para mais informações, confira a documentação a seguir.
Para que o kubectl use o novo plug-in binário na autenticação em vez do código padrão específico do provedor, siga as etapas abaixo.
- Depois de se conectar, execute o seguinte comando para instalar o
gke-gcloud-auth-pluginna VM.
- Configure
export USE_GKE_GCLOUD_AUTH_PLUGIN=Trueem~/.bashrc:
- Execute este comando:
- Execute o comando a seguir para forçar a atualização da configuração do cluster com a configuração do plug-in de credenciais do cliente Go.
Se tudo der certo, você vai receber esta mensagem:
O cluster recém-criado estará disponível para os comandos kubectl padrão no Bastion.
- Crie os namespaces, os papéis e as vinculações:
Saída:
Clique em Verificar meu progresso para conferir o objetivo.
Como gerenciar recursos com a conta de proprietário
- Abra um novo terminal do Cloud Shell clicando em + na parte de cima da janela do terminal.
Estabeleça a conexão SSH com a instância "owner" e crie uma implantação simples em cada namespace.
- Estabeleça a conexão SSH com a instância "owner":
-
Quando precisar indicar a zona, digite
npara usar a padrão. -
Instale gke-gcloud-auth-plugin:
- Crie um servidor em cada namespace, começando por
dev:
Saída:
- Depois crie
prod:
Saída:
- Por fim, crie
test:
Saída:
Clique em Verificar meu progresso para conferir o objetivo.
Como proprietário, você também poderá consultar todos os pods.
- Na instância "owner", liste os pods
hello-servernos namespaces executando o seguinte:
Saída:
Consultar recursos com a conta de auditor
Abra um novo terminal, estabeleça a conexão SSH com a instância "auditor" e tente verificar todos os namespaces.
-
Abra um novo terminal do Cloud Shell clicando em + na parte de cima da janela do terminal.
-
Estabeleça a conexão SSH com a instância "auditor":
-
Quando precisar indicar a zona, digite
npara usar a padrão. -
Instale gke-gcloud-auth-plugin:
- Na instância "auditor", liste os pods
hello-servernos namespaces executando o seguinte:
Você receberá este erro:
O erro indica que você não tem permissões suficientes. O papel de auditor é restrito à visualização dos recursos no namespace "dev". Por isso, você precisará especificar o namespace para ver os recursos.
Agora tente ver os pods no namespace "dev".
- Na instância "auditor", execute o seguinte:
Saída:
- Tente consultar os pods no namespace "test":
Saída:
- Tente consultar os pods no namespace "prod":
Saída:
Por fim, para verificar se o auditor tem acesso somente leitura, tente criar e excluir uma implantação no namespace "dev".
- Na instância "auditor", tente criar uma implantação:
Saída:
- Na instância "auditor", tente excluir a implantação:
Saída:
Tarefa 3: Cenário 2: atribuir permissões de API a um aplicativo de cluster
Neste cenário, você verá o processo de implantação de um aplicativo que requer acesso à API Kubernetes. Além disso, você irá configurar as regras do RBAC e solucionar alguns casos de uso comuns.
Como implantar o aplicativo de amostra
O aplicativo de amostra será executado como um único pod que recupera periodicamente todos os pods no namespace padrão do servidor de API e aplica um carimbo de data/hora a cada um deles.
- Na instância do admin (sua primeira guia do Cloud Shell), implante o aplicativo
pod-labeler. Isso também implantará um papel, uma conta de serviço e uma vinculação de papéis para o pod:
Saída:
Clique em Verificar meu progresso para conferir o objetivo.
Como diagnosticar uma configuração incorreta do RBAC
Verifique o status do pod. Após a criação do contêiner, aparecerá um erro. Investigue o erro examinando os eventos e os registros dos pods.
- Na instância admin, verifique o status do pod:
Saída:
- Na instância admin, execute o código abaixo e confira o fluxo de eventos do pod:
Você receberá:
- Para verificar os registros do pod na instância admin, execute o seguinte:
Saída:
Com base nesse erro, aparece um erro de permissão quando você tenta listar pods pela API.
- A próxima etapa é confirmar se você está usando a conta de serviço correta.
Como corrigir o nome da conta de serviço
Examine a configuração do pod e verifique se ele está usando a conta de serviço padrão, em vez da personalizada.
- Na instância admin, execute:
Saída:
O arquivo pod-labeler-fix-1.yaml contém a correção especificada no modelo da implantação:
Aplique a correção e verifique a mudança resultante.
- Na instância admin, aplique a correção 1 executando o seguinte:
Saída:
- Verifique a mudança na configuração da implantação:
Mudanças na resposta:
Clique em Verificar meu progresso para conferir o objetivo.
Como diagnosticar privilégios insuficientes
Ao verificar o status do pod novamente, você vai verificar que ele ainda apresenta um erro, mas agora com outra mensagem.
- Na instância admin, verifique o status do pod:
Saída:
Talvez seja necessário executar o comando anterior novamente para consultar essa resposta.
- Na instância admin, verifique os registros do pod:
Saída:
Como há falha em uma operação de PATCH, o erro também aparece no Stackdriver. Isso é útil quando os registros do aplicativo não têm níveis de detalhes suficientes.
-
No console, selecione Menu de navegação e, na seção "Operações", clique em Registros.
-
Na caixa de diálogo do Criador de consultas, cole o seguinte código e clique em Executar consulta:
- Clique na seta para baixo ao lado do registro e consulte os detalhes.
Identificar o papel e as permissões do aplicativo
Use a vinculação de papéis do cluster para encontrar o papel e as permissões da conta de serviço.
- Na instância admin, inspecione a definição
rolebinding:
Saída:
A definição RoleBinding mostra que você precisa inspecionar o papel pod-labeler no namespace padrão. Verifique neste exemplo que o papel só tem permissão para listar pods.
- Na instância admin, verifique a definição do papel
pod-labeler:
Saída:
Como o aplicativo requer permissões de PATCH, agora você o adicionará à lista "verbs" do papel.
O arquivo pod-labeler-fix-2.yaml contém a correção na seção "rules/verbs":
Aplique a correção e verifique a configuração resultante.
- Na instância admin, aplique
fix-2:
Saída:
Clique em Verificar meu progresso para conferir o objetivo.
- Na instância admin, confira a mudança resultante:
Saída:
Como pod-labeler talvez esteja em um loop de falha, a maneira mais rápida de testar a correção é eliminar o pod atual e deixar um novo assumir seu lugar.
- Na instância admin, execute o código abaixo para eliminar o pod atual e deixar que o controlador de implantação o substitua:
Saída:
Verificar a configuração
Por fim, verifique se o novo pod-labeler está em execução e se o rótulo "atualizado" foi aplicado.
- Na instância admin, liste todos os pods e confira os rótulos:
Saída:
- Verifique nos registros do pod se não há mais erros:
Saída:
Pontos-chave
- Nos registros do contêiner e do servidor de API, você encontra as melhores pistas para diagnosticar problemas do RBAC.
- Use "RoleBindings" ou "ClusterRoleBindings" para identificar o papel que está especificando as permissões do pod.
- Os registros do servidor de API estão localizados no recurso Kubernetes do Stackdriver.
- Nem todas as chamadas de API são registradas no Stackdriver. Os payloads frequentes ou detalhados são omitidos pela política de auditoria do Kubernetes usada no Kubernetes Engine. A política exata varia de acordo com a versão do Kubernetes, mas pode ser encontrada na base de código aberto.
Tarefa 4: Eliminação
Quando terminar e quiser limpar os recursos criados, execute este comando para removê-los:
-
Digite
exitpara sair do Bastion Host. -
Para excluir o ambiente, execute o seguinte comando:
Saída:
Clique em Verificar meu progresso para conferir o objetivo.
Tarefa 5: Solução de problemas no seu ambiente
Ocorre uma falha no script de instalação, e a mensagem Permission denied é exibida na execução do Terraform
As credenciais que o Terraform está usando não concedem as permissões necessárias para criar recursos nos projetos selecionados. Verifique se a conta listada em gcloud config list tem as permissões necessárias para criar recursos. Se tiver, gere novamente as credenciais padrão do aplicativo com gcloud auth application-default login.
Erro na validação da impressão digital em operações do Terraform
Durante a atualização de determinados recursos, o Terraform pode indicar que uma impressão digital é inválida. Execute novamente o comando se você receber um erro com a mensagem: Error: Error applying plan e depois liste estes erros:
module.network.google_compute_subnetwork.cluster-subnet: 1 error(s) occurredgoogle.compute_subnetwork.cluster-subnet: Error updating subnetwork/kube-net-subnet: googleapi: Error412: Invalid fingerprint, conditionNotMet
Parabéns!
Você aprendeu a usar o controle de acesso baseado em função (RBAC) atribuindo permissões diferentes aos perfis dos usuários e concedendo acesso limitado à API a um aplicativo em execução no seu cluster.
Termine a Quest
Este laboratório autoguiado faz parte da Quest Google Kubernetes Engine Best Practices: Security. Uma Quest é uma série de laboratórios relacionados que formam um programa de aprendizado. Ao concluir uma Quest, você ganha um selo como reconhecimento da sua conquista. Você pode publicar os selos com um link para eles no seu currículo on-line ou nas redes sociais. Inscreva-se nesta Quest ou em outra que tenha este laboratório para receber os créditos de conclusão imediatamente. Consulte o catálogo do Google Cloud Ensina para ver todas as Quests disponíveis.
Comece o próximo laboratório
Continue sua Quest com Segurança do Google Kubernetes Engine: autorização binária ou confira o conteúdo a seguir:
Próximas etapas / Saiba mais
- Configurar o controle de acesso baseado em função
- Criar políticas do IAM
- Autenticação de conta de serviço do Kubernetes
- Documentação do Terraform
Treinamento e certificação do Google Cloud
Esses treinamentos ajudam você a aproveitar as tecnologias do Google Cloud ao máximo. Nossas aulas incluem habilidades técnicas e práticas recomendadas para ajudar você a alcançar rapidamente o nível esperado e continuar sua jornada de aprendizado. Oferecemos treinamentos que vão do nível básico ao avançado, com opções de aulas virtuais, sob demanda e por meio de transmissões ao vivo para que você possa encaixá-las na correria do seu dia a dia. As certificações validam sua experiência e comprovam suas habilidades com as tecnologias do Google Cloud.
Manual atualizado em 9 de outubro de 2023
Laboratório testado em 9 de outubro de 2023
Copyright 2024 Google LLC. Este software é fornecido no estado em que se encontra, sem declarações nem garantias para qualquer uso ou finalidade. O uso do software está sujeito ao seu contrato com o Google.